hey guys,
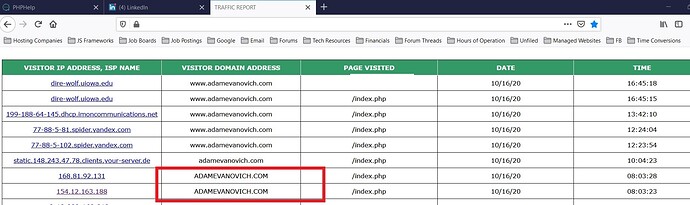
see attached image for what I’m questioning. I have traffic analysis code behind all of my pages. and a file that is ““included”” contains this code, among other lines:
$host = $_SERVER['HTTP_HOST'];
$page = isset($_SERVER['PHP_SELF']) ? $_SERVER['PHP_SELF'] : '';
the issue is that, sometimes when I view the log page, the PHP_SELF info that was captured comes through in all capital letters. and, sometimes too, in another bout of weirdness, the information is captured as ““mail.domain.com””. has anyone seen this before!? why would this happen? I’m guessing it’s a result of the endless amount of bot software running rampant on the internet, sourced from all different underground people the world over?
thanks.
Adam